So day 8 essentially was the last day of the bootcamp, with Day 9 + 10 being left for TSHOOT, of which there is very little documented, as its……. troubleshooting a broken system.
So Day 8, let’s get to it.
Here’s whats covered;
- HSRP Continued…..
- comparison between HSRP and VRRP
- GLBP – Gateway Load Balancing Protocol
- Port-Security
- Private VLANs
- AAA – Authentication, Authorization, Accounting
- VLAN Access-List
- DHCP Snooping
- ARP Poisoning / Man in the Middle
- IP Spoofing
- Other security considerations
- Logging
- MLS-Mutli-Layer Switching
- Process Switching
- Fast Switching
- CEF
- Voice – IP Telephony
- QoS – Quality of Service
- Layer 2 – Class of Service
- Layer 3 – IP Precedence (Old setting)
- Layer 3 – DSCP – Sub Marking (New setting)
- Configuration of QoS
- And that’s all folks
HSRP Continued…..
To enable tracking and failover of Virtual IP address;
Configuration on Active or First switch;
(config)#interface (value) (config-line)#standby (value) track (interface value) (decrement priority upon link failure) Example; (config-line)# standby 1 track fa0/48 51
So in the example above, imagine the first switches priority is 150, and the second switch is at default (100). If FA0/48 fails on the first switch, then the priority decrements by 51, which means the value is now 99. Which is less than Standby switch, which makes it now Active for the Virtual IP/Gateway.
To troubleshoot,
show standby
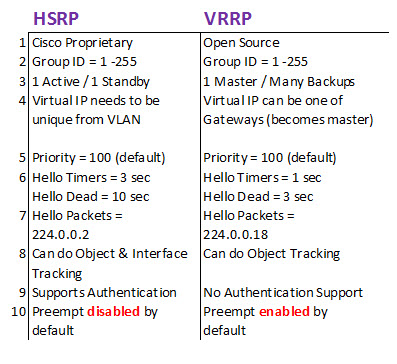
comparison between HSRP and VRRP
Configuration for VRRP
(config)#int vlan (value) (config-line)#vrrp (group id) ip (virtual ip and subnet) (config-line)#vrrp (group id) priority (value)
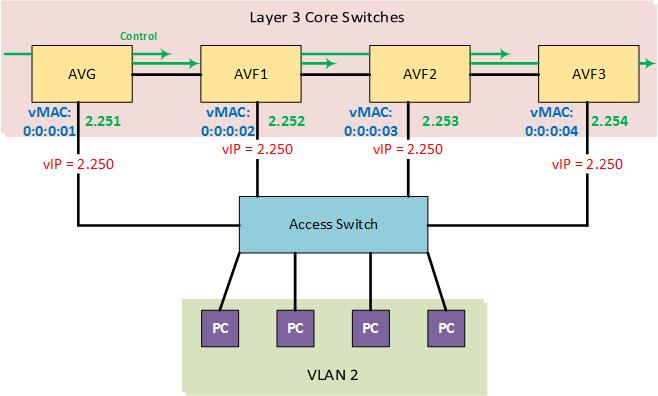
GLBP – Gateway Load Balancing Protocol
- Is a Cisco protocol
- Can do load balancing / sharing without need for multi-groups
- GLBP Process Number between 1 – 4095
The biggest limitation of HSRP and VRRP is that a single router (layer 3 switch) transits traffic for the whole group, leaving the others inactive until the master fails. GLBP solves this issue by load balancing traffic over up to four gateways, maximizing bandwidth.
One virtual IP is used, but each additional router (Layer 3 switch) uses a virtual MAC address which is used to respond to any ARP requests.
All Gateways above are active.
- AVG – Active Virtual Gateway (1 of)
- AFI – Active Virtual Forwarder (up to 3 of)
The AVG controls ARP & can decide route to exit the network by;
- Round Robin
- Weighted
- Host based
Port-Security
Configuration;
(config)#interface (value) (config-line)#switchport port-security (config-line)#switchport port-security max (value) (config-line)#switchport port-security mac-address (MAC value) OR (config-line)#switchport port-security mac-address sticky THEN (config-line)#switchport port-security violation (Shutdown/Protect/Restrict)
And to troubleshoot
#Show Port-Security
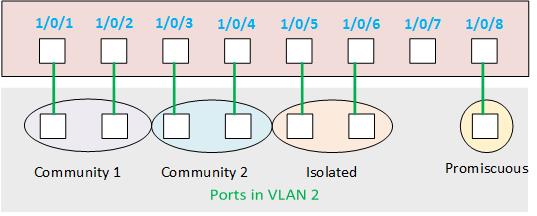
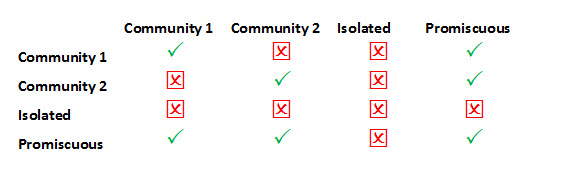
Private VLANs
Below is a table showing the communication paths
Notes;
- Watch for switch platform compatibility
- To configure, switch needs to be in VTP Mode – Transparent
Configuration;
This configures the private VLAN (config)#vlan (value) [EG. 202] (config-vlan)#private-vlan (community/isolated/primary) (config-vlan)#name (value) This configures the normal VLAN that Links to the Private VLAN (config)#vlan (value) [EG. 2] (config-vlan)#private-vlan primary (config-vlan)#private-vlan association (value) [EG. 201,202,203] Then on the interface (config)#interface (value) (config-line)#switchport private-vlan host (config-line)#switchport private-vlan host-association (vlan value) (Private-VLAN value) [EG. 2 201]
AAA – Authentication, Authorization, Accounting
Config process;
- AAA Service
- AAA –> Radius –> Server IP + Key
- AAA –> Dot1x Authentication
- Configure Switch as AAA client
- Verify Radius Server and AAA client communication
Configuration Commands;
(config)#aaa new-model (config)#aaa authenication dot1x default group radius (config)#radius-server host (IP address) key (key value) (config)#dot1x system-auth-control Then on the interface (config)#interface (value) (config-line)#dot1x port-control (auto <--[On Cisco 2950 switches]) (config-line)#switchport mode access
VLAN Access-List
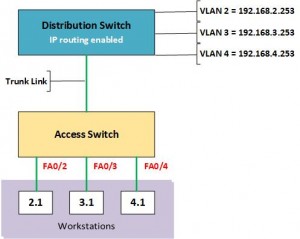
Here is the topology we will be using to create a VLAN ACL that;
- ObjectVLAN 2 is restricted
- VLAN 2 + 3 can converse
- All other VLANs cannot sent to VLAN 2
Configuration commands;
(config)#ip access-list standard (value) [Eg 10] (config-acl)#permit (ip address) (wildcard) [Eg 192.168.2.0 0.0.0.255] (config-acl)#permit (ip address) (wildcard) [Eg 192.168.3.0 0.0.0.255] (config-acl)#exit (config)#vlan access-map (name value) (number value) [Eg Lockdown 20] (config-vacl)#match ip address (number value)[Eg 10] (config-vacl)#action forward (config-vacl)#exit (config)#vlan access-map (name value) (higher number value) [Eg Lockdown 21] (config-vacl)# action drop (config-vacl)#exit (config)#vlan filter (name value) vlan-list (acl value) [Eg Lockdown, 10]
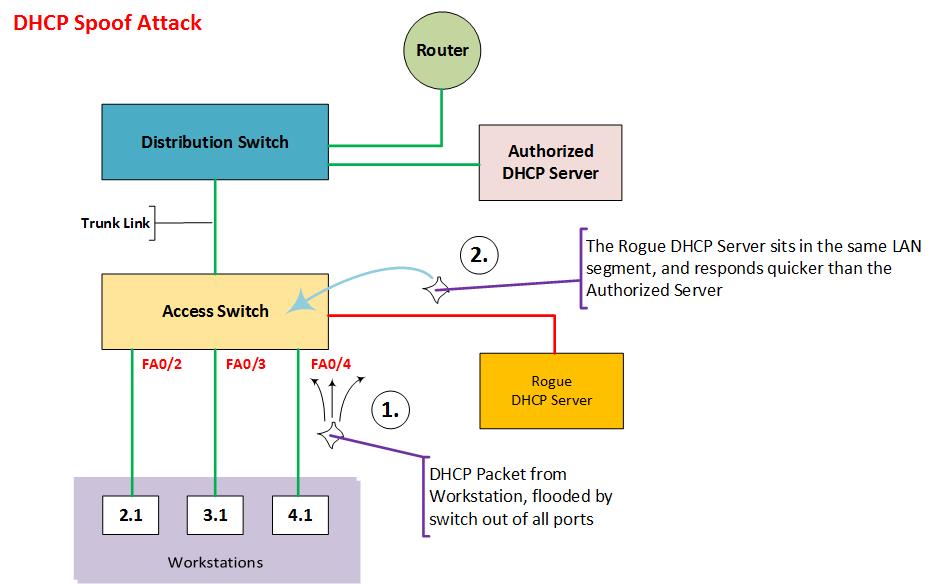
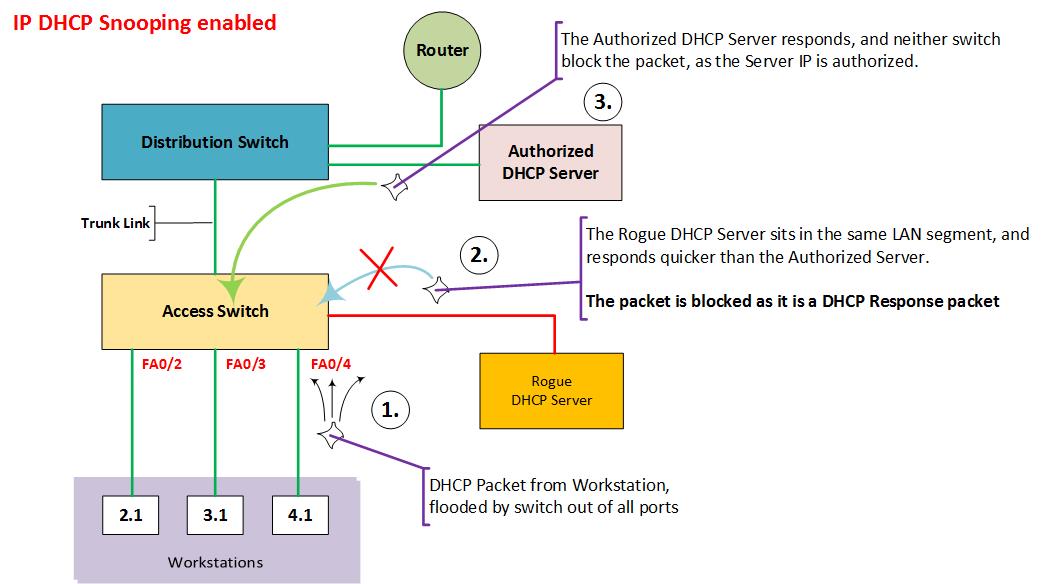
DHCP Snooping
Is the counter measure to stop DHCP Spoofing attack, (Command; ip dhcp snooping), defines all of the ports as untrusted, as such these ports can only handle (accept) DHCP client messages.
Therefore trunk ports, and the access ports connected to the authorized DHCP Server need to be trusted.
Untrusted ports can only receive discovery requests, and cannot receive acknowledgments.
Configuration;
(config)#ip dhcp snooping (config)#ip dhcp snooping vlan (value) (config)#interface (value) (config-line)#ip dhcp snooping trusted
The above config creates a binding table;
Interface – Source MAC – IP Address
FA0/1 – A:A:A:A -10.11.12.13
ARP Poisoning / Man in the Middle
Where ARP tables are injected with incorrect MAC Addresses. Mitigate with Dynamic ARP inspection (DAI).
Prerequisite; IP DHCP Snooping has to be enabled.
Configuration;
(config)#ip arp inspection vlan (value)
Port can only respond to an ARP that is in the binding table.
You need to trust Switch to Switch ports and Switch to Router ports.
Configuration of trust;
(config)#interface (value)
(config-line)#ip arp inspection trust
IP Spoofing
Where a rogue client duplicates an IP address of an existing legitimate host.
IP Source Guard feature makes reference to the DHCP Snooping Binding Table (So ip dhcp snooping must be enabled)
(config)#interface (value) (config-line)#ip verify source (vlan [value}) OR (dhcp-snooping) AND/OR (port-security)
Syntax;
- vlan applies the feature to only specific VLANs on the interface.
- dhcp-snooping option applies the feature to all VLANs on the interface that have DHCP snooping enabled.
- port-security enables MAC address filtering.
Other security considerations
- Disable CDP to inside interfaces of network devices, other than connected switches/routers.
- Prefer SSH, disable Telnet
- If using Telnet, setup Telnet Access-Lists
- Setup correct Username and Privilege levels
- Device hardening, features such as, auto-source and protect boot
Logging
0. Emergency 1. Alert 2. Critical 3. Error 4. Warning 5. Notice 6. Informational 7. Debug
Remove timestamps from logging (i.e logging to syslog);
(config)#no service timestamps debug uptime (config)#no service timestamps log uptime
Setup Netflow on interface;
(config)#interface (value) (config-line)#ip flow [ingress/egress]
Setup Netflow data to be sent to Server;
(config)#ip flow-export version (value [5]) (config)#ip flow-export destination (IP Address
Send logging to syslog;
(config)#logging trap (value [0,1,2 etc]) (config)#logging (ip address)
Setting up SNMP from device to Server;
(config)#snmp-server community (value) (config)#snmp-server location (value) (config)#snmp-server contact (value)
MLS – Mutli-Layer Switching
- CEF – Cisco Express Forwarding
3 types of L3 Switching;
- Process switching
- Fast switching
- CEF Cisco
- MPLS (Multi-Protocol Layer Switching) (Not layer 2, but be aware of the term)
Process Switching
Processor based forward,
Every packet that is routed is processed regardless of previous traffic. Every packet inspected before forwarding. Slowest method.
Fast Switching
Every 1st packet of a session is routed. While the rest are switched, every new session will result in the first packet being inspected, and a route cache is created.
Configuration;
(config)#ip route-cache
CEF
AKA Topology Based Routing.
Where the reference is made to the populated L3 information of the routing table to create a topological reference called the FIB (Forward Information Base).
The L2 information is referenced also (ARP Table) to form an Adjaceny table without the need to wait for every 1st packet that would be inspected.
Configuration;
(config)#ip routing (Pre-req; need to be enabled) (config)#ip cef Verifying #show ip cef (vlan)
Voice – IP Telephony
Call Manager
- Hardware based (CUCM Server -> HP)
- IOS Based (CME = Call Manager Express)
Gateway
- Device doing voice routing
Some more facts;
- Voice Packet (60-120 bytes)
- Delay needs to be under 150ms
- Drop of less than 1%
Voice call is typically 64kbps (8-106kbps for codec)
QoS – Quality of Service
Types;
- Best Effort (BE)
- Integrated Service (Reserved path bandwidth)
- Differential Service (Device decides best path)
1. Analyzing Traffic
- NBAR – Network Based Application Recognition
- Cisco default tool – IP Based
- IP CEF is pre-req
- Only shows a few protocols, for others need to download PDLM file and install.
- Netflow statistics can be pulled from device
Configuration;
(config)#ip routing
(config)#ip cef
(config)#interface (value)
(config-line)#ip nbar protocol discovery
Verify
#show ip nbar protocol discovery
2. Classification of analyzed traffic can divide the traffic into categories or classes, QOS uses class-map to do classification.
- Fruits
- Lemons
- Oranges
- Bananas
3. Marking is done on the categorised traffic at either Layer 2 or Layer 3 level;
- Layer 3 – Class of Service (802.1p) – Marking happensonL2 switch/IP phones
- IP Precedence (old setting)
- DSCP – Differential service code point (new setting)
- Remarking happens on L3 Switch/Router
Layer 2 – Class of Service
7. Reserved 6. Reserved 5. Voice 4. Video Conference 3. Call Signalling 2. High Priority Data 1. Medium Priority Data 0. Best Effort
Layer 3 – IP Precedence (Old setting)
7. Reserved 6. Reserved 5. Voice 4. Video Conference 3. Call Signalling 2. High Priority Data 1. Medium Priority Data 0. Best Effort
Layer 3 – DSCP – Sub Marking (New setting)
Configuration of QoS
(config)#interface (value) (config-line)#mls qos trust cos (config)#interface (value)i (config-line)#mls qos trsut device-cisco-phone
And that’s all folks
And that covers it for now, I’ll type up a summary post pulling all the days together, tidy up any errors and diagrams that are missing or need tweaks.
Do get in touch if you have any issues with this material or suggestions of improvements.
Dean (LinkedIn)