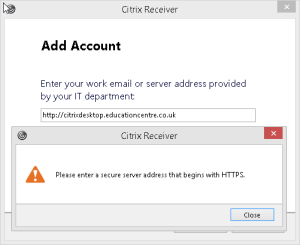
The latest versions of Citrix receiver require that you use HTTPS for the server bound connections, otherwise you cannot connect.
And the information on the Citrix website can be a bit thin when it comes to using a Public CA SSL Certificate. Here is the documentation link to using certificates for the Storefront component.
Here I am covering;
- Workaround – Bypassing the HTTPS SSL warning when adding a store to Citrix Receiver
- Creating the Public SSL Certificate request for your StoreFront Server
- Importing the Public SSL Certificate onto your StoreFront Server
- Exporting the SSL Certificate for use on additional servers
- Linking the SSL Certificate in IIS to the StoreFront Website
Workaround – How to bypass this restriction
You can follow this Citrix KB here.
Complete the following changes in the registry:
- For 32-bit Windows – HKEY_LOCAL_MACHINE\SOFTWARE\Citrix\Dazzle
- For 64-bit Windows – HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Citrix\Dazzle
Change the following ReyKey
REG_SZ: AllowAddStore
Value: A
Note: Changing the value to A allows to add non-secure URLs.
Creating the Public SSL Certificate Request
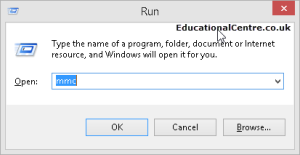
Log in as an administrator of your StoreFront Server
- Open a run dialog box, type mmc and click OK.
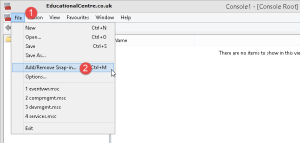
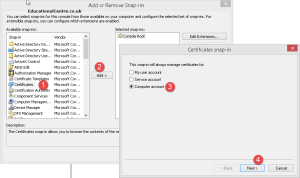
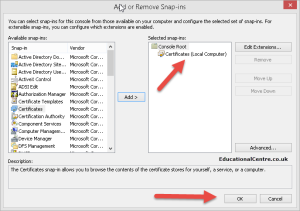
- On the File menu, click Add/Remove Snap-in. Click Certificates in the left pane, then click Add.
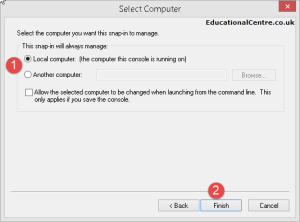
- Select Computer Account, then click Next.
- Select Local Computer, then click Finish.
- Click OK.
It is recommended that you do this using the local machine store
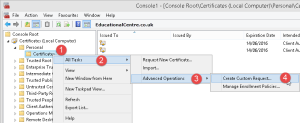
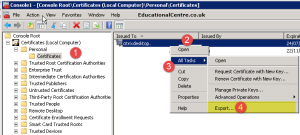
- Expand Certificates (Local Computer), expand Personal, then click Certificates.
- Right Click on the Certificates folder > All Tasks > Advanced Operations, click Create Custom Request.
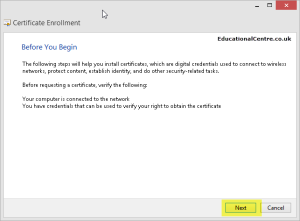
- Click Next.
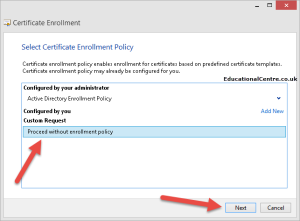
- Select Proceed without enrollment policy. Click Next.
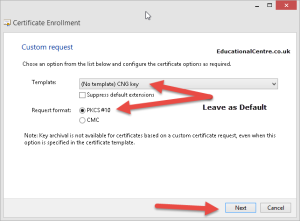
- Leave the template settings as the default. Click Next.
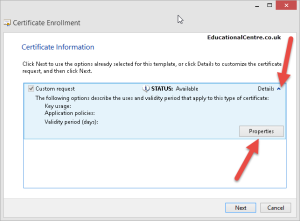
- Click the arrow next to Details to expand the selection. Click Properties.
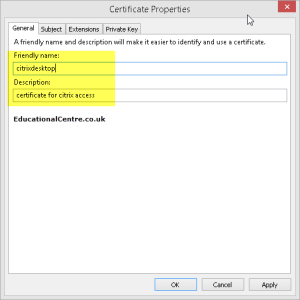
- On the General tab, provide a Friendly name and Description for the certificate. (This can be anything you like).
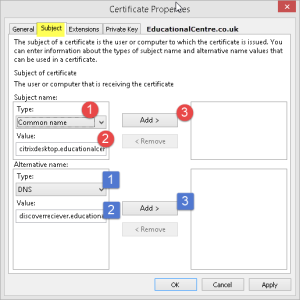
- On the Subject tab, in the Subject name box:
- In the Type menu, select Common name. In the Value field, type the fully qualified domain name that you want (e.g. citrixdesktop.educationalcentre.co.uk), and click Add.
- select Organization. In the Value field, type University of Washington.
- select State. Add your Value
- select Country. Add your Value
You many want to add additional names to the certificate. If you want to use the email discovery for citrix receiver you need to add “discoverreceiver.yourdomainname.etc” On the Subject tab, in the Alternative name box, enter subject alternative names if you need them (these can also be requested when you submit the CSR).
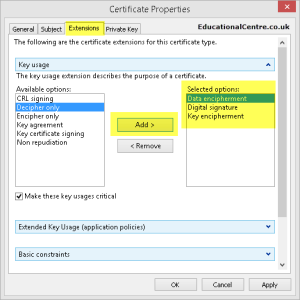
To restrict how this certificate can be used, you can select the appropriate options under Key usage and Extended Key Usage on the Extensions tab. Below I selected the options that appeared on the self signed certificate that was created.
- Data encipherment
- Digital signature
- Key encipherment
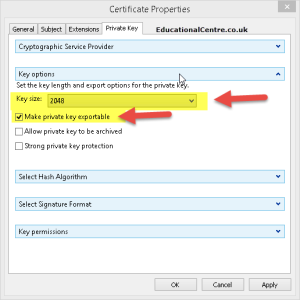
- On the Private Key tab, expand Key Options.
- In the Key size drop down, select a value of at least 2048.
- Select Make private key exportable.
- Click OK.
- Click Next on the Certificate creation screen
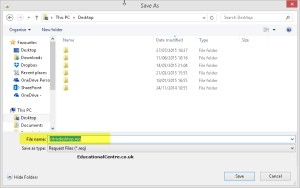
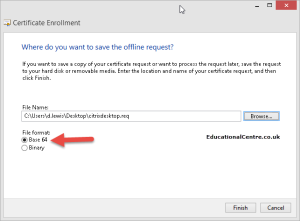
Choose a file name and location for the CSR. Select Base 64. Click Finish.
Submit the CSR file to your chosen Public SSL Provider
Importing the Public SSL Certificate onto your StoreFront Server
- Download your Public SSL Certificate onto the server that you created the request from.
- Open up the MMC and Certificate snap-in as above
- Go to Personal > Certificates > Right Click >All tasks > Import
- Browse for your certificate
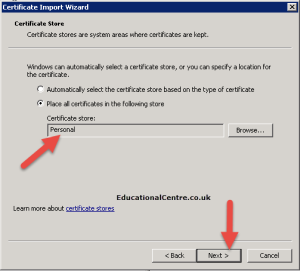
- Select the “Personal” certificate store
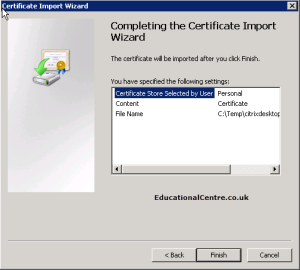
- Click finish
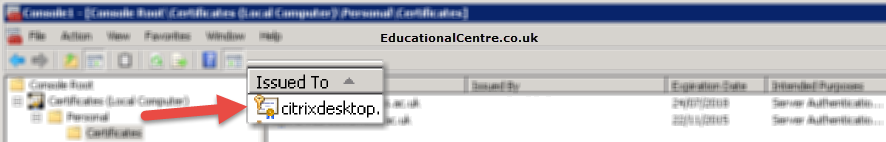
You can see now that the certificate is available and there is a key symbol next to it, if not, then you probably have not selected the exportable key option in the SSL request.
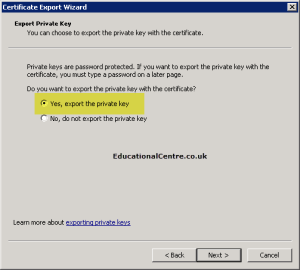
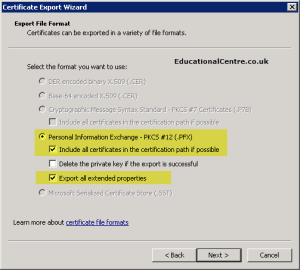
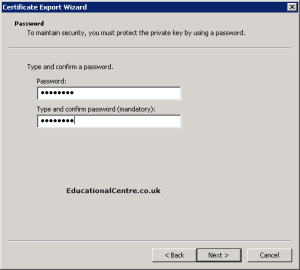
Exporting the SSL Certificate for use on additional servers
- In the Certificate Snap-in, find your certificate, right click and select Export.
- Select the setting to export the key and extended properties
- Set the password
- Set your save location (this will be a p7x file)
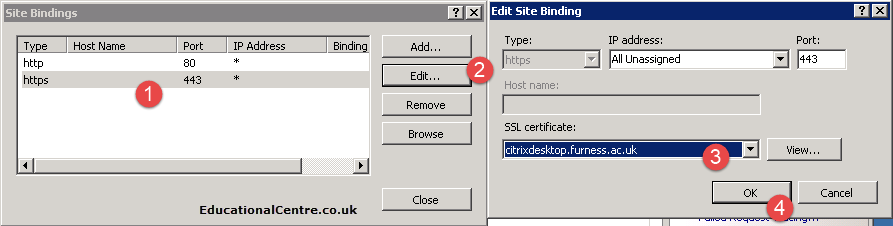
Linking the SSL Certificate in IIS to the StoreFront Website
- On your StoreFront server, open up IIS Manager.
- Click on the default site
- Open up the bindings
- edit the https/443 settings
- select the certificate
Dean Follow @saintdle