Following on from my previous blog post;
We will now continue and deploy our first Workload (Guest) Cluster into Azure for us by our developers to deploy their applications into.
For this technical walkthrough, I am assuming you have followed the previous blog post and have the Tanzu CLI and Kubectl CLI installed, and a working management cluster.
As a reminder of the terminology;
- Tanzu Kubernetes Workload Clusters
Once you have deployed your management cluster, you can deploy additional CNCF conformant Kubernetes clusters and manage their full lifecycle. These clusters are designed to run your application workloads, managed via your management cluster. These clusters canrun different Kubernetes versions as required. These clusters use Antrea networking by default.
These types of clusters are also referred to as “workload” clusters, or “guest” clusters, with the latter typically referring to the Tanzu Kubernetes Grid Service running in vSphere.
Deploying a Guest Cluster
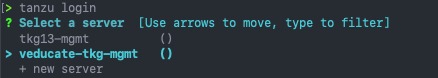
Login to your Tanzu environment Management Cluster with the following:
Tanzu login
First we need to create a cluster configuration YAML file. You can find a template here for Azure, or view the full available variables here.
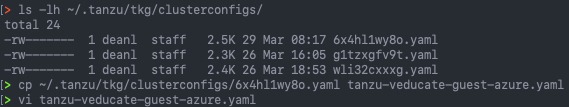
Alternatively, we can use the existing YAML file in our ~/.tanzu/tkg/clusterconfigs folder used for the management cluster deployment and change a few settings to make it ready for our workload guest cluster.
This was my preferred method as it contained all my Azure settings already.
#Find existing cluster config file # Tanzu 1.3 Location ls -lh ~/.tanzu/tkg/clusterconfigs/ # Tanzu 1.4 location ls -ls ~/.config/tanzu/tkg/clusterconfigs/ #Copy file to a new config cp ~/.tanzu/tkg/clusterconfigs/6x4hl1wy8o.yaml tanzu-veducate-guest-azure.yaml # Edit file = CLUSTER_NAME # Workload cluster names must be 42 characters or less.
 Continue reading Deploying Tanzu Kubernetes Grid Workload Cluster to Microsoft Azure
Continue reading Deploying Tanzu Kubernetes Grid Workload Cluster to Microsoft Azure