This blog post will cover managing a number of Folding@Home Clients using FAHControl.
If you are using the VMware F@H Fling, then this appliance will be configured for remote control on deployment.
This blog is based on Folding@home deployed on Linux, but the same applied for Windows.
Installing FAHControl to monitor multiple installations
For Windows instances, this is installed as part of the FAHClient
- “C:\Program Files (x86)\FAHClient\FAHControl.exe“
For Linux, you will need to install FAHControl separately
For Mac OS X Instances, this is installed as part of the FAHClient
- Applications > Folding@Home > FAHControl
Configuring your FAHClient for remote access
On your deployed OVAs
- Connect via SSH
- Edit the config.xml file
- vi /etc/fahclient/config.xml
- Insert the following code to enable FAHControl access
- From within vi press ‘i’
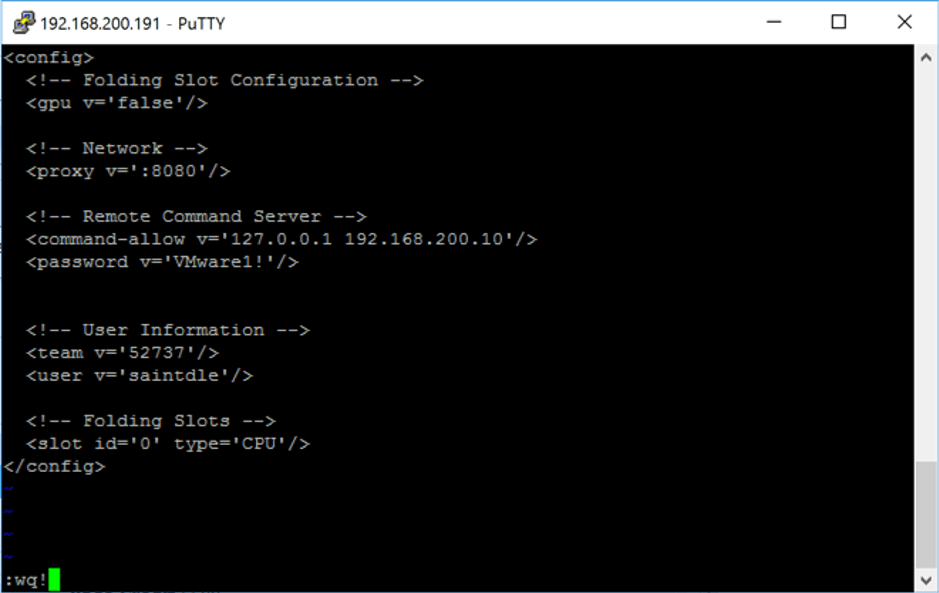
- To configure a single address to access your client
- Without passwords;
<command-allow-no-pass v='127.0.0.1 x.x.x.x’ />
- With Password;
<command-allow v='127.0.0.1 192.168.200.10' /> <password v='VMware1!' />
N.B. The localhost address must remain configured, otherwise the client work run
Examples:
Using password with a single IP restriction
<!-- Remote Command Server --> <command-allow v='127.0.0.1 192.168.200.10' /> <password v='VMware1!'/>
Without a password against a single IP restriction
<!-- Remote Command Server --> <command-allow-no-pass v='127.0.0.1 192.168.200.10' />
Without either a password or IP restriction
<!-- Remote Command Server --> <command-allow-no-pass v='127.0.0.1 0.0.0.0/0' />
- Save the config.xml file
- Press ESC key
- Enter without quotes “:wq!”
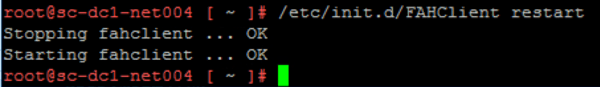
- Reload the FAHClient
- /etc/init.d/FAHClient restart
If you see “Starting fahclient … FAIL” check your XML file again for any syntax errors.
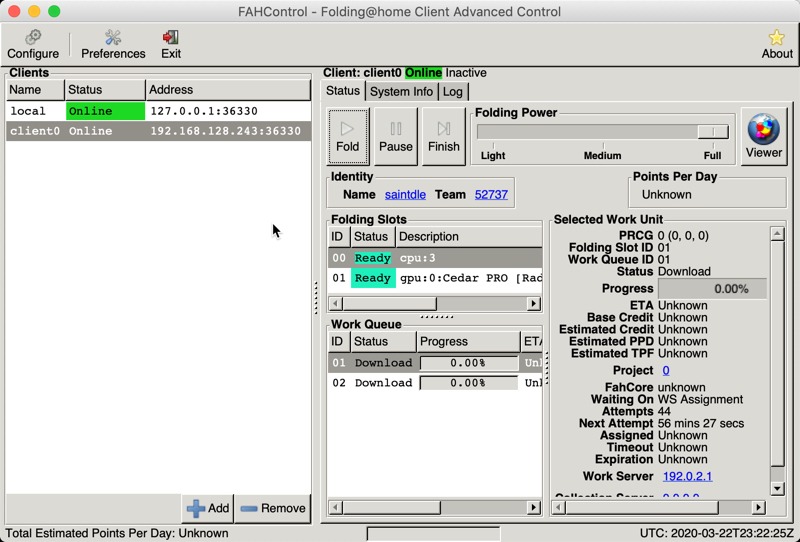
Connecting FAHControl to your clients
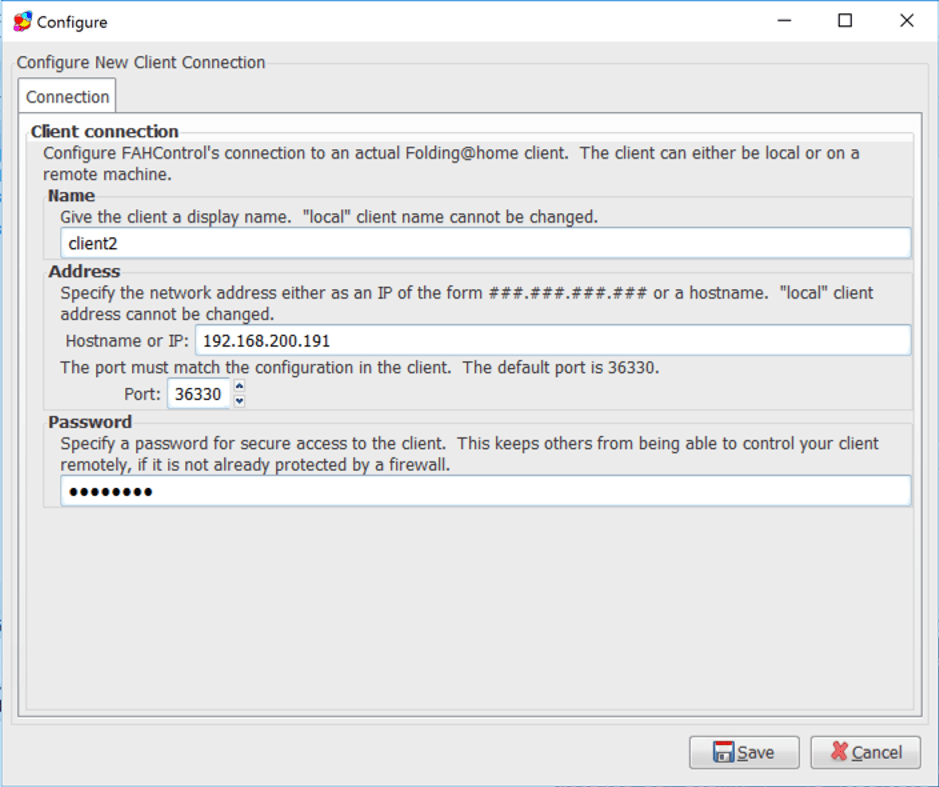
- Open your FAHControl and click Add
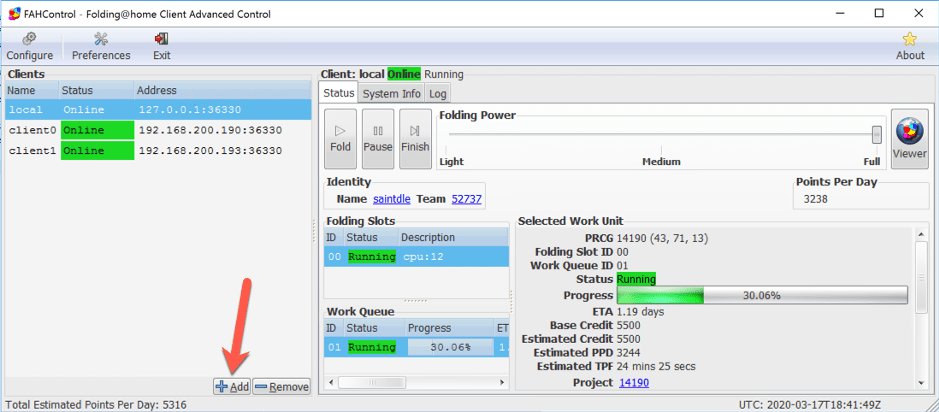
- Enter the name of your client as you would like it to be displayed, the IP address of your client and your password if necessary, and click save.
- You should now see your client is connected in FAHControl.
Appendix
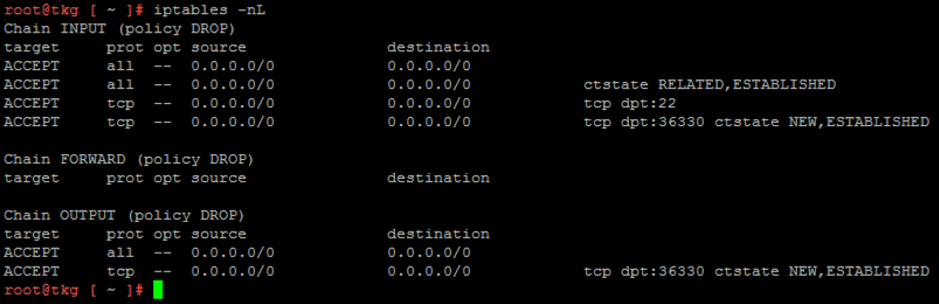
Firewall rules
If you are using iptables, the below firewall rules will need to be configured for Linux allow for FAHControl to remotely manage FAHClient.
iptables -A INPUT -p tcp --dport 36330 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT iptables -A OUTPUT-p tcp --dport 36330 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT
Regards