As part of some internal lab work, I had to move the user objects with their passwords to a new forest. It was key to migrate the passwords to ensure that disruption to the users was minimized.
To migrate the users, I used the Microsoft Active Direction Migration Tool (ADMT + documentation) alongside the Password Migration Service.
In this blog post I am going to cover;
- Create connectivity between both AD Forests
- Installing the ADMT software + Password Migration Service
- Creating a user list for migration
- Migrating User objects + Passwords between AD Forests
Create connectivity between both AD Forests
There must be IP network connectivity between the DC’s in your Forests.
DNS setup
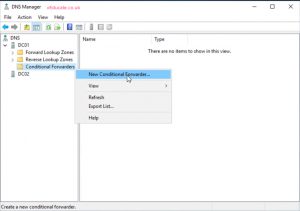
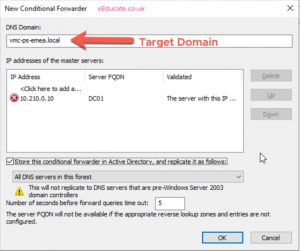
You need to configure conditional forwarders between your forests, so they can resolve one another.
On the source domain controller;
- Open up the DNS console, and right click the Conditional Forwarder folder to create a new record.
- Enter your target domain name and IP address/es of your domain controllers in the target domain. Select “store this conditional forwarder in active directory”, to replicate to other DCs in the source domain.
 Continue reading Migrating User and Password Objects between Active Directory Forests
Continue reading Migrating User and Password Objects between Active Directory Forests